Cloud and Data SecurityUnvalidated Redirects — Web-based Application Security, Part 1
Understanding open redirection vulnerabilities is key to detecting them and protecting your organization’s data. Without proper validation, attackers can redirect victims from trusted to malicious sites, or use forwards to access unauthorized pages.
By
Brian Rutledge
3 minute read
Web application security, which applies specifically to the security of websites, web applications and web services, is increasingly becoming a top priority for organizations worldwide. To understand why, consider that one in four organizations has experienced a web app breach in the past 12 months. In fact, a 2018 software security report noted that more than 85% of web apps have at least one security vulnerability. Understanding these vulnerabilities is key to detecting them and protecting your organization’s data. In this series on Web Security, we analyze the major vulnerabilities plaguing organizations starting with Unvalidated Redirects.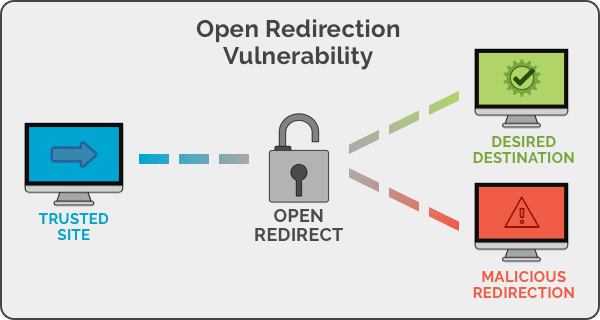 ## Understanding the Unvalidated Redirects Vulnerability
## Understanding the Unvalidated Redirects Vulnerability
The Open Web Application Security Project (OWASP) — the gold standard for web security — describes an Open Redirection as follows: “Web applications frequently redirect and forward users to other pages and websites, and use untrusted data to determine the destination pages. Without proper validation, attackers can redirect victims to phishing or malware sites, or use forwards to access unauthorized pages.”
On the surface, redirecting a user to a given website or page may seem like a harmless action. However, it can be misused to have a serious impact as it gives the hacker an open door to infect your network/website and steal customer credentials. This can put your organization’s web presence, data and credibility into jeopardy.
In Action: Unvalidated Redirects or Forwards
Let’s examine some examples in which redirects or forwards can be easily exploited.
Consider that your organization’s website has a redirect to a trusted partner site. Your valid URL will be:

This can be manipulated with code that adds an HTTP 302 redirect to a malware site – with a similar looking URL:

Another common redirect is the login page. In this example, after a user logs in to the website, they are redirected to their account information page:

These are only some manifestations of an unvalidated redirect. The redirect could be to a login screen where an unsuspecting user enters their credentials, or to a malicious executable, or a ransomware link. Additionally, the URL can be easily obfuscated, to even pass detection from an alert user. Not only will the user’s data be stolen, but your organization’s reputation will be severely damaged.
For instance, eBay, a secure and well-established site, had fallen victim to this vulnerability. eBay’s open redirect below allowed redirects to any URL.
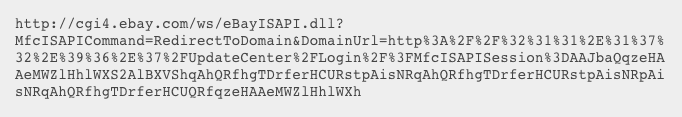
This was used by a hacker to redirect to a phishing site that mimicked eBay’s login page; thereby stealing the user’s eBay credentials. The URL was obfuscated to avoid detection by the user.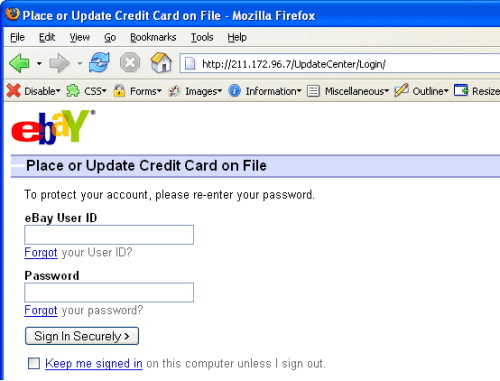 ## Preventing the Unvalidated Redirects Vulnerability
## Preventing the Unvalidated Redirects Vulnerability
Redirects are easy to exploit, but the vulnerabilities are easy to detect too. Here are some tips to keep in mind.
Avoid Redirects, Or Else Encrypt
Design your app to avoid URL redirects or forwards as a best practice. If unavoidable, encrypt the target URL such that the URL:token mapping is validated on the server.
Validate all URLs
Verify URL patterns using regular expressions to check if they belong to valid URLs. However, malicious URLs can pass that check. Therefore, add another check where URLs are vetted against a whitelist: a list of valid URLs.
Check your Referrers
Links to your website from an external source can also be infected. Social media, in particular, has upped the ante, owing to the ubiquitousness of links in shares, tweets, etc. Also, as social URLs are typically truncated, they can be easily manipulated.
Stay tuned for Understanding Cross-Site Forgery, the next topic in our Web-based Application Security blog series.
Secure your SaaS Data with Spanning