Cloud and Data SecuritySaaS Data Encryption: Data at Rest vs Data In-Transit
SaaS data encryption involves having state of the art encryption at rest and encryption in-transit. The right SaaS backup can provide security to data whether data is at rest or data is in-transit.
By
Dave Wallen
3 minute read
SaaS applications like Google Workspace and Microsoft 365 have delivered unparalleled benefits to businesses. These include reduced overheads, increased productivity, easy accessibility, and more. But on the other hand, unprotected data stored in these SaaS applications leaves your business vulnerable to data loss. Add to that, SaaS companies are responsible for securing their infrastructure and not your data that is stored in it. It is not surprising that two out of three businesses are victims of SaaS data loss. Businesses have realized SaaS applications cannot be treated as the sole beacon of light when it comes to securing their data. To offset this, they are choosing backup solutions that offer advanced SaaS data encryption whether the data is at rest or in-transit.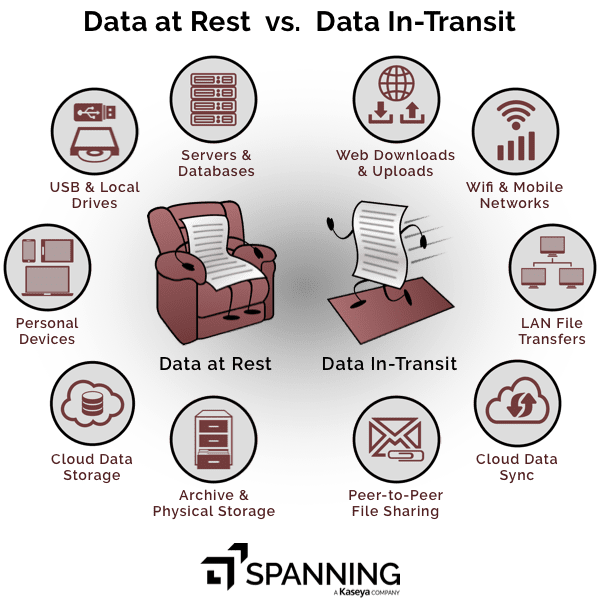 ## What is data at rest?
## What is data at rest?
Data at rest is data which is not actively moving within the system or network and does not interact with any third-party applications such as data stored in hard drives, mobile phones, flash drives, laptop, etc.
Attackers will eye for data at rest if your SaaS applications are unable to provide strong at-rest encryption standards. This results in the repeated unauthorized distribution of sensitive data.
Imagine, someone gets their hands on your phone with the intention of accessing your inbox to sneak peek into your business emails! If your SaaS vendor lacks strong encryption at-rest, thieves can access confidential information living on those emails.
What is data in-transit?
In-transit means ‘in motion’ or simply put, data moving from one location to another. It includes data traveling from network to network or data transfer from local storage to cloud storage.
Data in motion is often considered less secure and its vulnerability makes it a sweet spot for attackers. It puts you and other parties that do business with you at risk. Knowing your SaaS application can provide encryption in-transit is a must.
Interestingly, one of the most frequently asked questions for our reps in on Spanning’s encryption standards. There is a sigh of relief when they learn Spanning uses the 256-bit AES object-level encryption that secures data and generates encryption keys as well.
Robust Data Protection with the Right SaaS Backup
A good backup and recovery solution bridges the security gap that appears between SaaS applications and businesses. With advanced SaaS data encryption standards, countermeasures are created for both data in rest and in-transit. Essentially, threats can be neutralized before they cause any real damage with proactive data protection.
However, a wrong backup solution does the opposite. It not only fails to protect business-critical data but also brings in new threats, putting your data — and your business — at risk.
Download our whitepaper Securing Your SaaS Backup to develop a comprehensive security strategy for your SaaS backup.
Ask the right questions – find the right answers – choose the right SaaS backup.
Get the Whitepaper